負担を減らしても、
安心は減らない。
それが、これからの
本人認証です。
安全を保つには、負担がつきもの。
そう思ってはいませんか。
企業もユーザーも、
本当は「ラクで安全」がいちばんうれしい。
そんな理想を叶えるのが、DZ Securityです。
独自の「バックグラウンド認証®」で、
ログイン不要ながらも安全な本人認証を実現。
ユーザーの手間だけではなく、
企業の個人情報の保持コストと
偽装・流出リスクを減らします。
強固かつあらゆる負担が少ない認証技術で、
サービスをもっと自由に。
私たちはそのサポートをいたします。
DZ Security® の特徴
企業もユーザーも、ログインや登録に関わる負担なく
安全にサービスが利用できるようになる革新的な本人認証システムです。
1バックグラウンド認証®で、
あなたのサービスをログイン不要に。
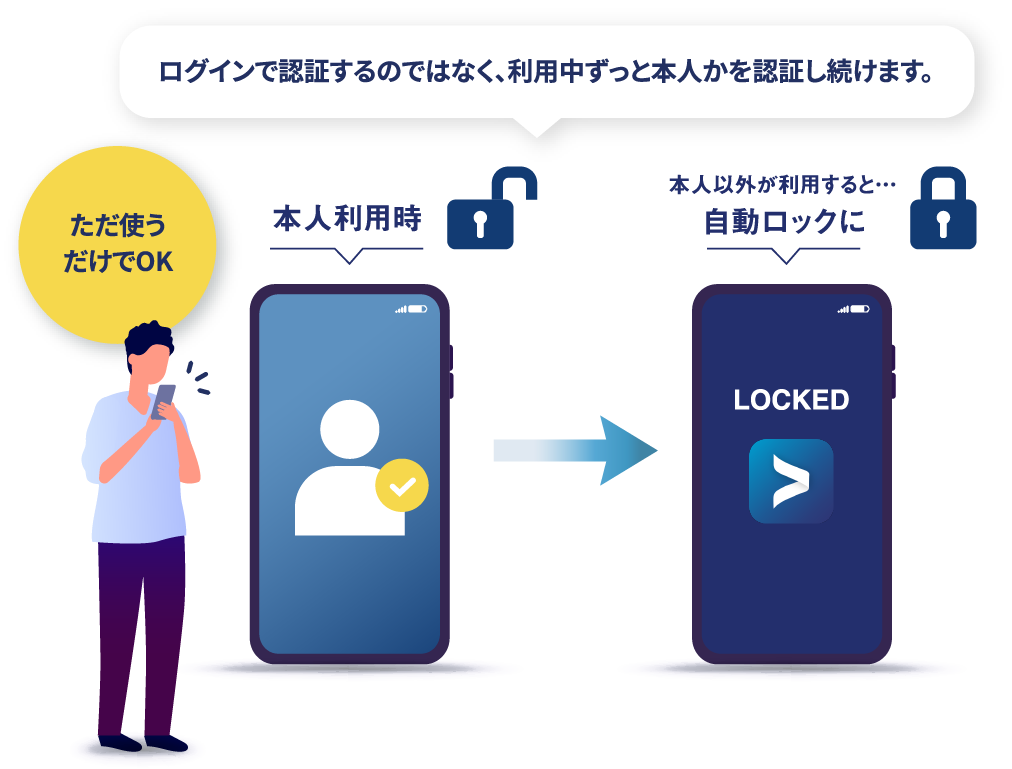
これまでの本人認証では、IDとパスワードを入力してログインするのがあたりまえでした。しかしそれでは、ログイン後も同じ本人が使い続けているかどうかはわかりません。そこで私たちは、まったく新しい発想の認証技術を開発しました。スマートフォン利用時に自然に習得することができる顔や声の生体情報、さらにはふるまい情報(デバイス利用時のクセ)など、複数の要素をバックグラウンドで随時認識。デバイス利用者が登録者本人かどうかを随時適宜、認証し続け、ログインにとらわれることなく「なりすまし」の脅威を防ぎます。
「バックグラウンド認証®」とは?
利用者本人の「顔」か
利用者本人の「声」か
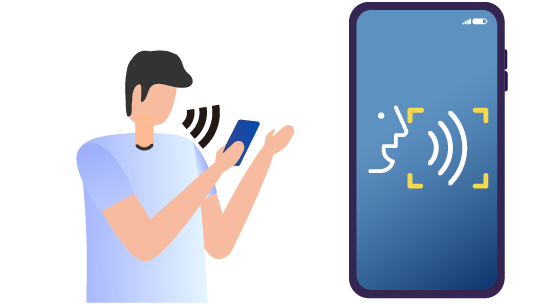
利用者本人の「ふるまい」※か
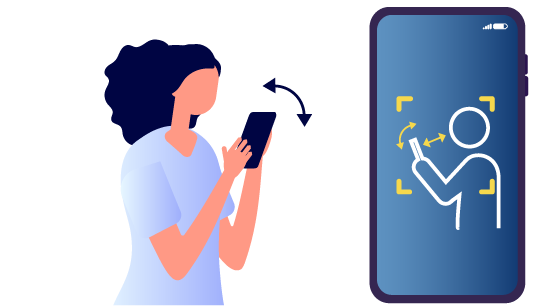
「複数の生体情報」に加えて「ふるまい情報」を統合し、バックグラウンドで随時認識し続けることで、利用中ずっと本人かどうかを確認し続ける世界初の本人認証技術です。
※ ふるまいの例
・デバイスと目の距離
・デバイスの傾け方
などの個人特有のクセ
2パスワードなどの個人情報の
保持サーバーが不要に。
バックグラウンドで認証しつづけるため、ログインするという考え方がなくなり、IDとパスワードが不要に。また、認証に使われる複数のデータはすべて利用者の端末内に保存されるため、サービス側における個人情報の保持サーバーが不要になります。個人情報を管理する負担を減らしながら、その漏洩の心配もなくなります。

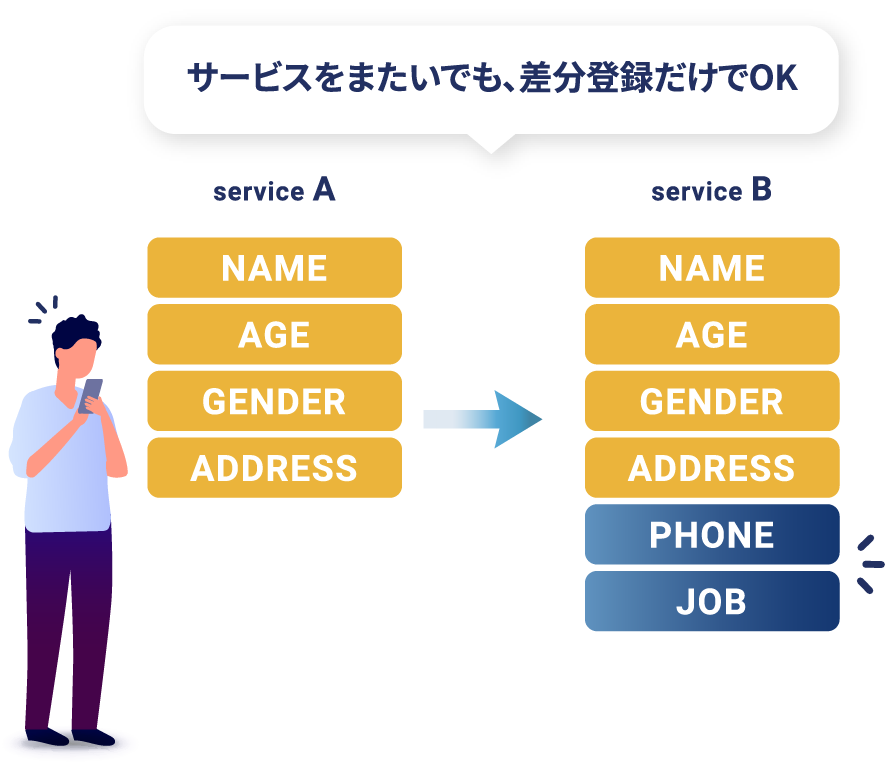
3DZ Security®の活用サービス同士なら
情報登録の二度手間が不要に。
プラットフォームサービス「DZ Intelligent Access Platform®(DZ IAP®)」 を使えば、DZ Security®を活用するサービス同士で、利用者本人を特定しながらユーザーの登録情報の共有が可能になります。だからサービスをまたいでも、ユーザーは差分だけの登録でOK。より快適なサービス体験を提供することができるようになります。
国際特許を取得済み
上記の技術に関して、特許を取得しました。
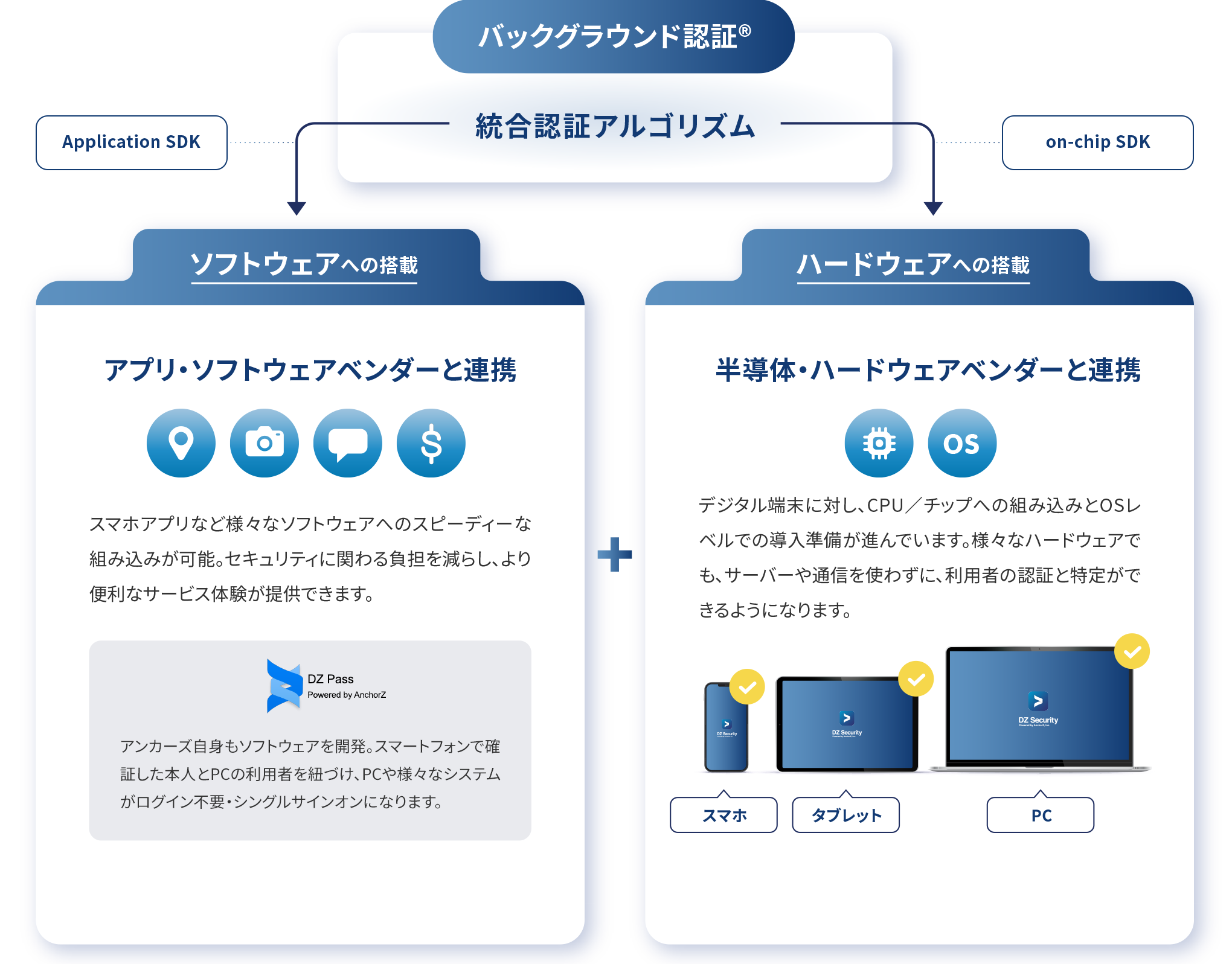
独自の国際特許技術である「統合認証アルゴリズム」をコア技術として、製品開発しています。
ご利用可能な端末
スマートフォン・タブレット・PC、どのデバイスでもご利用いただけます。
導入事例
DZ Security®
が目指すイノベーション
世界初の本人認証技術「バックグラウンド認証®」をコア技術に、
ハードウェア・ソフトウェア様々なベンダー企業と共に、より便利で安心な本人認証のイノベーションを目指します。

ログインや登録に関わる本人認証の負担を減らす
ログイン不要に!

DZ Intelligent Access Platform®
(DZ IAP®)
発行された唯一性識別子で個人を識別しながら、DZ Security®の活用サービス同士で情報連携ができるプラットフォームサービスです。サービス利用時の本人登録をサービス毎に何度も行う必要が無くなります。
ユーザー本人を鍵とし
様々なサービスが本人確認で分断されない、
より自由で便利な世界へ
ABOUT私たちについて

本人認証の負担と不安をなくす
徳山 真旭
株式会社AnchorZ(アンカーズ)は、独自の特許技術に基づいたソフトウェア製品を開発・提供するメーカーです。「本人認証の負担と不安をなくす」ことを掲げ、誰もが簡単に使えて、情報の偽装・漏洩リスクもない、安心と負担のジレンマを終わらせるセキュリティのイノベーションを目指しています。
AnchorZ 企業サイトTOP へ